How DNS Resolution Works
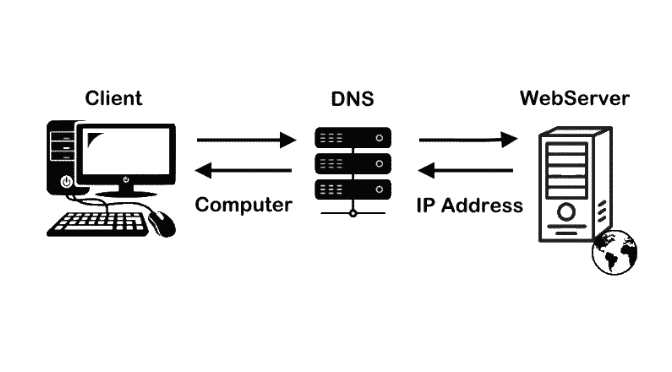
What is DNS and why name resolution exists
DNS stands for Domain Name System. DNS is used to map human-readable names to IP-addresses. DNS are useful because it is easier for us as humans to remember names rather than specific IP addresses to our favorite website, this is where DNS comes in to play, converting the names into IP-addresses. Without DNS, users would have to remember number of the IP address. DNS acts like a universal phonebook, people’s names are replaced with website names and telephone numbers are replaced with IP-addresses, only it is not accessible to us as is. Name resolution in DNS simply means converting domain names into IP addresses.
What is the dig command and when it is used
The dig command is a powerful DNS inspection tool that helps users query DNS servers to find out detailed information about domain name resolutions. This command is used in the terminal. When you run a command like dig google.com, you are asking the DNS servers to provide information on how to resolve the domain name google.com into its IP address. The output of the dig command has various sections, like the question section, answer section, authority section and additional section, each providing specific details about the DNS query and response process.
The dig command is used to
Debug DNS issues.
See which servers answer queries
Understand the resolution flow.
Understanding dig . NS
The command dig . NS is used to identify the Root Name Servers that sits at the top of the DNS hierarchy. The specific . is used to select the root DNS and requesting for the NS (Name server) records. These root server do not know IP addresses. When this command is run, it return the 13 logical root servers that act as the starting point for resolving any web address. Root servers guide the resolver, they don’t resolve domains themselves.
Understanding dig com NS
While dig . NS looks at the top of the hierarchy, dig com NS focuses specifically on the Top Level Domain(TLD) servers related to .com. When this command is run, you are looking for authoritative name servers that manage all domains ending with .com. These servers act as the middle man in the DNS hierarchy, they don’t know the IP address of a specific site like google.com but they know exactly which name servers have that information. This is the second layer in DNS resolution.
Understanding dig google.com NS
Running the command dig google.com NS is the final level in the DNS hierarchy, the Authoritative Name Servers. Unlike the root or TLD servers, these specific servers hold the actual IP address for a particular domain. When you run this command, you are asking the internet, that which specific servers are the ones that manage the records for google.com. The answer points to Google’s own infrastructure like ns1.google.com which is where all specific records like IP addresses(A records) are stored and managed. These servers are the source of truth and the final answers come from here.
Understanding dig google.com
When you run a standard dig google.com without NS, you are asking for the full DNS resolution flow to find a specific IP address. Instead of asking who is in-charge of a server, you are asking for the A record, the actual location of the server.
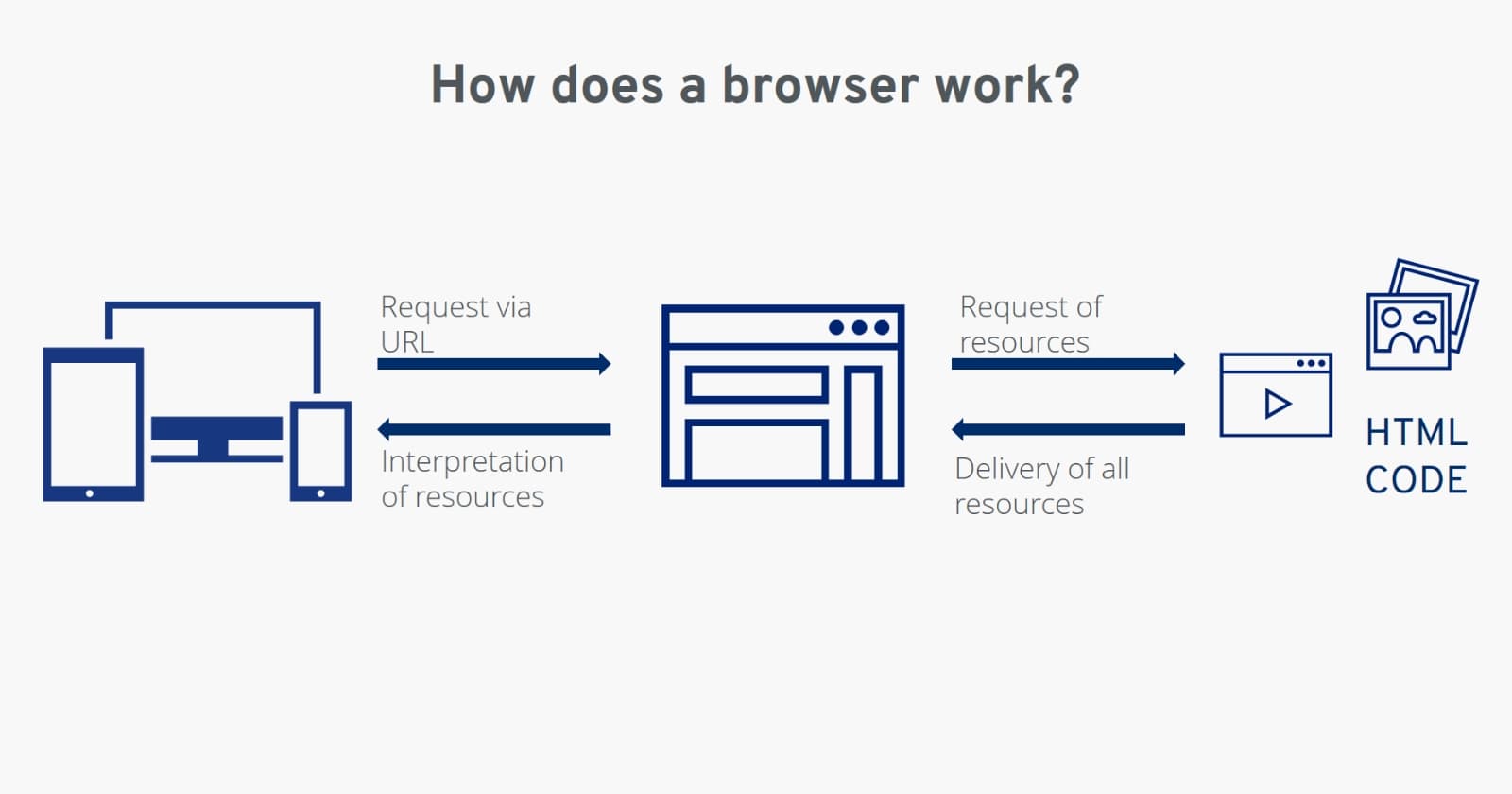
The entire flow is shown in the diagram below.

The Full Resolution Flow is as follows:
Client asks recursive resolver.
Resolver queries root servers.
Root servers point to TLD(.com)
TLD points to google.com authoritative servers.
Authoritative servers return IP address.
Resolvers caches the result for later usage.
Client connects to IP.
Conclusion:
DNS Hierarchy is a structured phonebook that is used to delegate the traffic from the general servers to specific ones. Using dig at different levels allows you to see this personally. Understanding this flow is the key to troubleshooting why a website might be reachable for few people but appear to be down for others due to propagation or configuration errors.